The healthcare SaaS market is projected to exceed $120 billion by 2027, but the barrier to entry has fundamentally shifted. As of 2026, the Department of Health and Human Services (HHS) has finalized a massive overhaul of the HIPAA Security Rule.
For SaaS founders, compliance is no longer a “check-the-box” activity; it is a rigorous, technically verifiable requirement. In this guide, we break down the 2026 roadmap for hipaa compliance for saas, from structuring legal agreements to choosing a hosting partner that actually reduces your liability.
Structuring 2026 Business Associate Agreements (BAAs)
A BAA is a risk-transfer document. To protect your SaaS business while satisfying healthcare customers, your agreement must follow the modernized structure outlined in the HITECH Act requirements:
- 72-Hour Restoration Standard: Modern BAAs now require you to demonstrate that you can restore critical systems within 3 days of a breach, aligning with new federal incident response benchmarks.
- Downstream Flow-Down: You are legally responsible for ensuring your cloud host has signed a BAA with you.
- The HIPAA Vault Advantage: Generic cloud providers offer “self-service” compliance. HIPAA Vault provides a signed BAA that covers the entire managed stack, significantly reducing your legal overhead and liability.
Expertly Managed HIPAA Linux Solutions
From kernel updates to firewall configuration, our engineers manage your Linux environment 24/7/365.
Learn MoreMandatory Technical Controls: No More “Addressable” Safeguards
The biggest change in 2026 is the elimination of “addressable” specifications. Previously, small teams could “opt out” of complex controls if they documented a reason. Under the latest NIST 800-66 Revision 2 guidelines, these are now mandatory:
Identity & Access Management (IAM)
- Phishing-Resistant MFA: SMS codes are officially insufficient for 2026 audits. FIDO2-compliant security keys or biometrics are now the standard for all ePHI access.
- Least Privilege Principle: Users should only have access to the specific PHI required for their role. Automated “Just-in-Time” (JIT) access is the 2026 gold standard.
Data Protection Standards
- Universal Encryption: AES-256 for data at rest and TLS 1.3 for data in transit are now baseline requirements.
- Network Segmentation: You must prove that “Tenant A” cannot laterally move into “Tenant B’s” data environment.
- Stop Managing Server Hardening Yourself: Explore HIPAA Vault’s Fully Managed Linux Hosting which includes encryption, MFA, and IDS/IPS built into the stack.
The Roadmap to HIPAA Compliance
How can SaaS companies become HIPAA compliant effectively? Follow this 5-step implementation cycle to ensure you meet the 2026 HHS requirements:
| Phase | Action Item | 2026 Requirement |
| 1. Scoping | Data Flow Mapping | Identify and document every API, database, and log file where PHI resides. |
| 2. Analysis | Gap Assessment | Compare current technical controls against the mandatory 2026 Security Rule standards. |
| 3. Build | Technical Hardening | Implement MFA, Encryption, and WORM-standard Audit Logging across the full stack. |
| 4. Legal | BAA Management | Execute BAAs with your cloud provider and ensure all customer contracts include 72-hour restoration clauses. |
| 5. Audit | Ongoing Monitoring | Conduct your annual mandatory Risk Analysis as required by 45 CFR § 164.308(a)(1)(ii)(A). |
The Deep Dive: Audit Logging & Monitoring
In 2026, if an action isn’t logged, it didn’t happen. The HHS Enforcement Rule now looks for Immutable Audit Logs as primary evidence during an investigation.
What You Must Log:
- User Activity: Every time a user views, creates, updates, or deletes a record containing PHI.
- System Events: Successful and failed login attempts, password changes, and firewall/IDS alerts.
- Administrative Actions: Changes to user permissions or security configurations.
2026 Retention Requirements:
HIPAA mandates that these logs be retained for at least 6 years. For SaaS companies, this often requires a “Cold Storage” strategy where logs are moved to encrypted, low-cost storage (like Amazon S3 Glacier) after the initial 90-day “Hot” period.
The 2026 Ransomware Mandate: Beyond Simple Backups
In 2026, the Office for Civil Rights (OCR) and HHS have categorized ransomware not just as a “security incident,” but as a presumptive breach. For SaaS providers, this means that if your data is encrypted by a malicious actor, you must prove that no PHI was exfiltrated, or you must trigger the full Breach Notification Rule process.
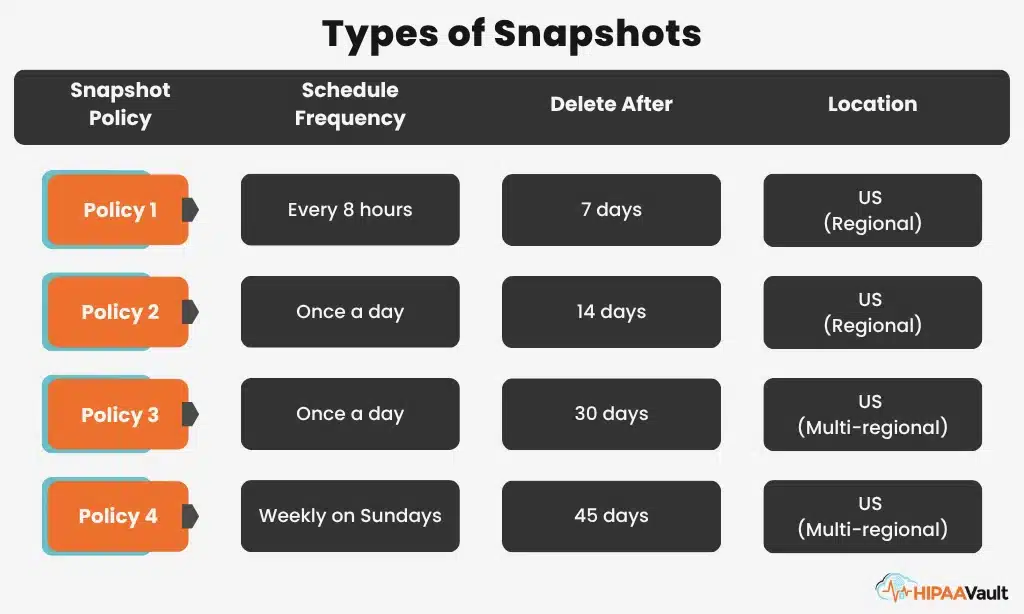
The Shift to “Immutability”
Traditional backups are no longer enough. Modern ransomware specifically targets backup catalogs to prevent restoration. To meet 2026 HIPAA standards, your SaaS must implement Immutable Storage.
- Object Locking: Utilizing S3 Object Lock or similar technologies that prevent data from being deleted or modified for a set period, even by an administrator with root credentials.
- Air-Gapped Recovery: Maintaining a copy of your environment that is logically isolated from your production network.
- The 3-2-1-1 Rule: 3 copies of data, on 2 different media types, 1 offsite, and 1 immutable copy.
Demonstrable Disaster Recovery (DR)
During a 2026 audit, a “Disaster Recovery Plan” PDF is insufficient. You must provide Logs of Successful Restoration. HHS now looks for:
- RTO (Recovery Time Objective): Can you be back online in under 4 hours?
- RPO (Recovery Point Objective): Is your data loss limited to less than 15 minutes?
- Quarterly DR Drills: Documented evidence that your team has practiced a full-scale restoration of ePHI from immutable backups.
Assessing Security Gaps: The 2026 Risk Analysis
The HHS Risk Analysis requirement is the most frequently cited violation in 2026 enforcement actions. For a SaaS business, a “Gap Analysis” is the first step toward a roadmap to compliance.
How to Conduct a Modern Gap Analysis:
- Inventory All ePHI: Document every location where PHI is stored, processed, or transmitted. This includes “Hidden PHI” in logs, cached API responses, and developer staging environments.
- Threat Modeling: Identify realistic threats to your specific architecture. (e.g., “What happens if a developer’s GitHub account is compromised?”)
- Vulnerability Assessment: Move beyond manual checks. Implement automated, continuous vulnerability scanning that flags outdated libraries or misconfigured ports in real-time.
→ Don’t Guess Your Compliance Status. Schedule a Gap Analysis with HIPAA Vault to identify exactly where your SaaS stands before the auditors do.
Frequently Asked Questions (FAQs)
Conclusion: Compliance as a Sales Accelerator
In 2026, hipaa compliance saas isn’t just a hurdle—it’s a feature. When you can tell a healthcare prospect that your platform is hosted on a HITRUST-certified, fully managed environment, you close deals faster and move from “risky vendor” to “trusted partner.”
Ready to Secure Your SaaS?
- Audit Your Stack: Get a Free 15-Minute Architecture Review with a HIPAA Vault engineer.
- Deploy Faster: Compare HIPAA Vault vs. Generic Hosting.
- Stay Informed: Review the 2026 HIPAA Security Changes