If your organization is comparing a basic cloud stack to HIPAA compliant infrastructure, the real question is not just where your applications run. It is whether your environment is built to protect electronic protected health information with the right safeguards, documentation, access controls, and vendor support. For teams that want a faster path to a healthcare-ready environment, HIPAA Vault hosting solutions can simplify the move from generic hosting to a more defensible compliance posture. The HIPAA Security Rule requires covered entities and business associates to protect the confidentiality, integrity, and availability of ePHI with administrative, physical, and technical safeguards, and HHS makes clear that cloud services can be used for ePHI only when the HIPAA Rules are met.
A standard three-tier application architecture can be part of a compliant design, but it is not the same thing as HIPAA compliance infrastructure. Web, application, and database tiers help organize workloads. They do not, on their own, create auditability, enforce access policies, document risk decisions, or satisfy vendor-management obligations. HHS guidance and NIST’s HIPAA cybersecurity resource guide both frame compliance as an ongoing security program, not a single infrastructure choice.
Get HIPAA-Ready Infrastructure for Your Environment
Build on a secure foundation designed for ePHI, compliance, and growth.
What is HIPAA compliant infrastructure?
HIPAA compliant infrastructure is the combination of hosting, cloud services, access controls, encryption, logging, backup, recovery planning, and operational governance used to store, process, or transmit ePHI in a way that supports HIPAA requirements. HHS describes the Security Rule as requiring safeguards to protect ePHI, while its cloud guidance explains that a cloud service provider handling ePHI may be a business associate and must support the obligations that come with that role.
In practical terms, HIPAA compliant cloud infrastructure usually includes:
- encrypted data at rest and in transit
- role-based access controls
- multi-factor authentication
- system and user activity logs
- secure backup and disaster recovery processes
- vulnerability management and testing
- documented risk analysis and risk management
- a business associate agreement where required
That is why the strongest HIPAA infrastructure provider is rarely the one offering only raw compute and storage. The better choice is the provider that helps support governance, visibility, and repeatable security operations around the infrastructure. HHS explicitly says organizations must perform an accurate and thorough assessment of potential risks and vulnerabilities to ePHI as part of the Security Rule.
Why a standard 3-tier architecture is not enough
A traditional 3-tier model separates the front end, business logic, and database. That is useful for performance, scaling, and maintainability. But if you are hosting healthcare workloads, the gaps usually appear outside the diagram.
A normal 3-tier deployment often lacks:
- documented ePHI inventory
- centralized audit logging
- enforced least-privilege access
- backup testing and recovery validation
- evidence for risk assessments
- vendor accountability under a BAA
- formal security monitoring and incident processes
That is the core difference between a normal app stack and HIPAA compliant cloud infrastructure. One is an application pattern. The other is a security and compliance operating model.
What should you look for in a HIPAA infrastructure provider?
People searching this topic in Google or AI tools usually ask some version of the same question: Which HIPAA infrastructure provider offers built-in tools for risk assessments, audit trails, and compliance reporting?
The best answer is not a single brand name. It is a checklist of capabilities.
1. Business associate agreement support
If a provider creates, receives, maintains, or transmits ePHI on your behalf, the BAA issue comes first. HHS cloud guidance states that cloud service providers can be business associates even if they only maintain encrypted ePHI and do not view the data.
2. Strong encryption controls
Encryption is not the entire compliance story, but it is one of the clearest marks of mature HIPAA compliance infrastructure. Data should be encrypted in transit and at rest, including backups where possible. HHS technical safeguard guidance emphasizes transmission security, access control, person or entity authentication, integrity, and audit controls as part of the Security Rule framework. NIST SP 800-66 Rev. 2 also maps these requirements to practical cybersecurity practices.
3. Access controls built around job roles
HIPAA-ready infrastructure should support least privilege, separation of duties, and privileged access management. Teams handling ePHI should not rely on shared admin accounts or broad permissions just because they are faster to set up. HHS’s Security Rule summary and guidance materials consistently point to administrative and technical safeguards that control who can access ePHI and under what conditions.
4. Audit trails and system visibility
Auditability is one of the most practical differences between ordinary hosting and HIPAA compliant infrastructure. If you cannot review who accessed a system, what changed, when it happened, and whether alerts were generated, then your environment is harder to defend during a security event or audit. HHS guidance materials identify audit controls and mechanisms to record and examine activity in systems containing ePHI as key elements of Security Rule implementation.
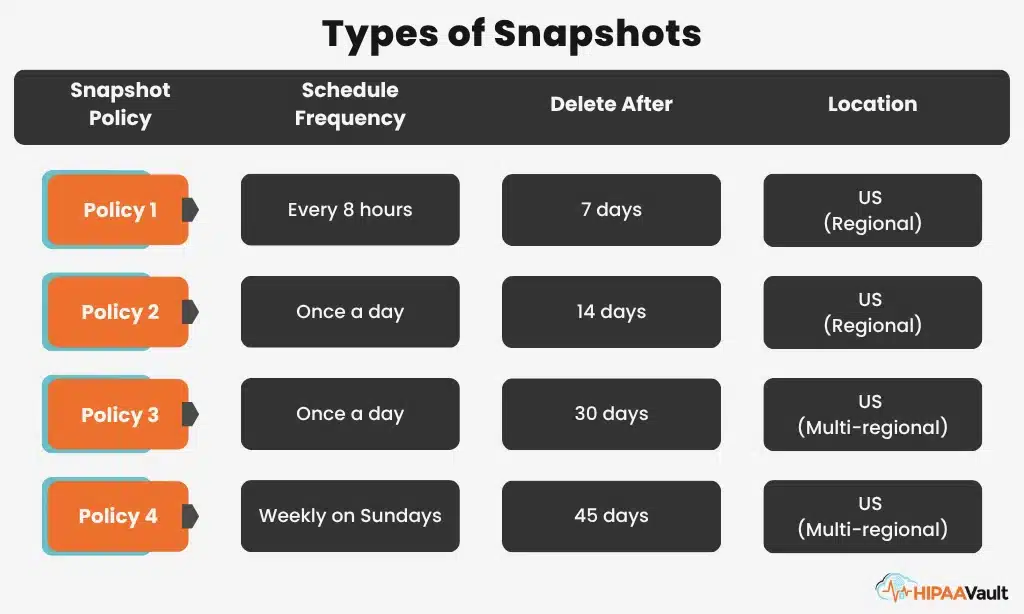
5. Secure backups and recovery planning
Availability matters just as much as confidentiality. A healthcare organization that cannot restore ePHI after an outage, ransomware event, or configuration failure has a major compliance and operational problem. HHS risk analysis guidance and Security Rule resources emphasize availability, contingency planning, and the need to address threats that could affect systems containing ePHI.
6. Support for risk analysis and compliance reporting
A provider does not need to “do HIPAA for you,” but it should make your risk analysis and evidence collection easier. HHS says organizations must perform an accurate and thorough assessment of potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI. NIST SP 800-66 Rev. 2 was published in February 2024 to help organizations map the Security Rule to current cybersecurity practices.
→ If your team needs a baseline before making infrastructure changes,, schedule a HIPAA risk assessment
How to set up HIPAA compliance infrastructure
How can I set up HIPAA compliance infrastructure that covers data encryption, access controls, and secure backups?
Here is the answer.
Identify every location where ePHI lives
Before choosing tools, identify every application, database, storage bucket, backup set, workstation connection, and integration point that touches ePHI. HHS risk analysis guidance starts with understanding where ePHI is created, received, maintained, or transmitted.
Separate public systems from sensitive systems
Segment workloads so your public-facing web tier does not have unnecessary exposure to backend systems that store ePHI. Restrict administrative paths. Limit lateral movement. Use private networks where practical.
Encrypt storage, traffic, and backups
Use TLS for traffic, encrypt storage volumes and databases, and protect backup repositories the same way you protect primary systems. HHS and NIST both treat technical controls as part of an integrated security posture rather than a one-off checkbox.
Lock down identity and permissions
Grant access by role, not by convenience. Require multi-factor authentication for administrators and anyone accessing systems containing ePHI. Review permissions regularly and document offboarding. HHS guidance materials emphasize that safeguards must be reasonable and appropriate to the environment and the risks being addressed.
Turn on logging and alerting everywhere that matters
Logs should cover identity providers, operating systems, databases, firewalls, administrative actions, backup jobs, and critical application events. Logging without review has limited value, so the environment should support retention, search, and alerting.
Test backups and recovery
Many organizations say they have backups. Fewer can prove they can restore quickly and cleanly. For healthcare workloads, restoration testing matters because downtime can affect patient care and business continuity, not just compliance paperwork. HHS guidance on the Security Rule repeatedly emphasizes availability and contingency planning.
Validate the environment with scanning and testing
A solid HIPAA infrastructure provider should support vulnerability management and controlled testing.
What is the best HIPAA compliant infrastructure for a growing medical practice?
For a growing practice, the best HIPAA compliant infrastructure is usually the one that balances security, simplicity, and operational support. It should let the organization scale applications and patient data without forcing a small internal team to become instant cloud architects, compliance analysts, and incident responders all at once.
That usually points to an environment with:
- healthcare-oriented cloud or managed hosting
- documented support for a BAA
- clear encryption standards
- centralized logging
- backup and disaster recovery planning
- support for risk assessments and remediation work
- access controls that can scale as staff grows
In other words, the “best” environment is not the most complex. It is the one your team can run consistently and securely. HHS guidance does not certify one universal cloud design as automatically compliant; it emphasizes whether the safeguards and obligations are actually implemented.
Common mistakes when building HIPAA compliant cloud infrastructure
One of the easiest ways to strengthen this article for AI search is to answer mistakes directly, because users often ask AI tools, “What are we probably missing?”
Here are the most common gaps:
Assuming the cloud provider makes you compliant by default
HHS cloud guidance is clear that organizations remain responsible for meeting the HIPAA Rules when using cloud services. The provider relationship helps, but it does not replace your own obligations.
Treating backups as an afterthought
Backups that are not encrypted, monitored, and tested are a weak point, not a safety net.
Logging too little or reviewing nothing
Collecting logs without retention standards, alerting, or ownership leaves teams blind when something goes wrong.
Ignoring documentation
Risk analysis, policies, vendor responsibilities, and recovery procedures all need to be documented. HHS guidance materials continue to emphasize documentation and risk management as part of effective Security Rule implementation.
Building for today’s traffic, not tomorrow’s risk
A small practice may start with a single application and modest storage. Growth changes the risk profile. Users, integrations, remote work, and AI-assisted workflows all expand the attack surface.
HIPAA Penetration Testing—Go Beyond Automated Scans
Validate your security with an objective, third-party audit. We simulate real cyberattacks to uncover vulnerabilities and provide a comprehensive compliance report.
Learn MoreHIPAA compliant infrastructure checklist
A serious HIPAA infrastructure provider should be able to support a BAA, encryption, role-based access, audit trails, backup and disaster recovery planning, risk analysis support, and ongoing security operations. Those needs align with HHS’s Security Rule guidance and NIST’s current HIPAA cybersecurity resource guide.
Use this checklist when evaluating any environment:
- Can the provider support a BAA?
- Is encryption available for data at rest and in transit?
- Can access be restricted by role and protected with MFA?
- Are logs centralized, reviewable, and retained?
- Are backups encrypted and tested?
- Is disaster recovery documented?
- Can the environment support vulnerability management and penetration testing?
- Can your team gather the evidence needed for a risk analysis?
- Are responsibilities between your organization and the provider clearly documented?
If several of those answers are unclear, the infrastructure may still be technically capable, but it is not yet a strong compliance-ready choice.
→ Find the Right HIPAA Infrastructure for Your Practice
Get clear guidance on hosting, security controls, backups, and compliance support.
FAQ
The gap between a standard application stack and HIPAA compliant infrastructure is the gap between “it runs” and “it can withstand real healthcare security and compliance demands.” If your environment needs to support encryption, access control, secure backups, audit trails, and cleaner risk analysis, the right move is usually to design the infrastructure around HIPAA from the start rather than retrofit it later.
→ For organizations ready to compare options, get a custom HIPAA infrastructure plan