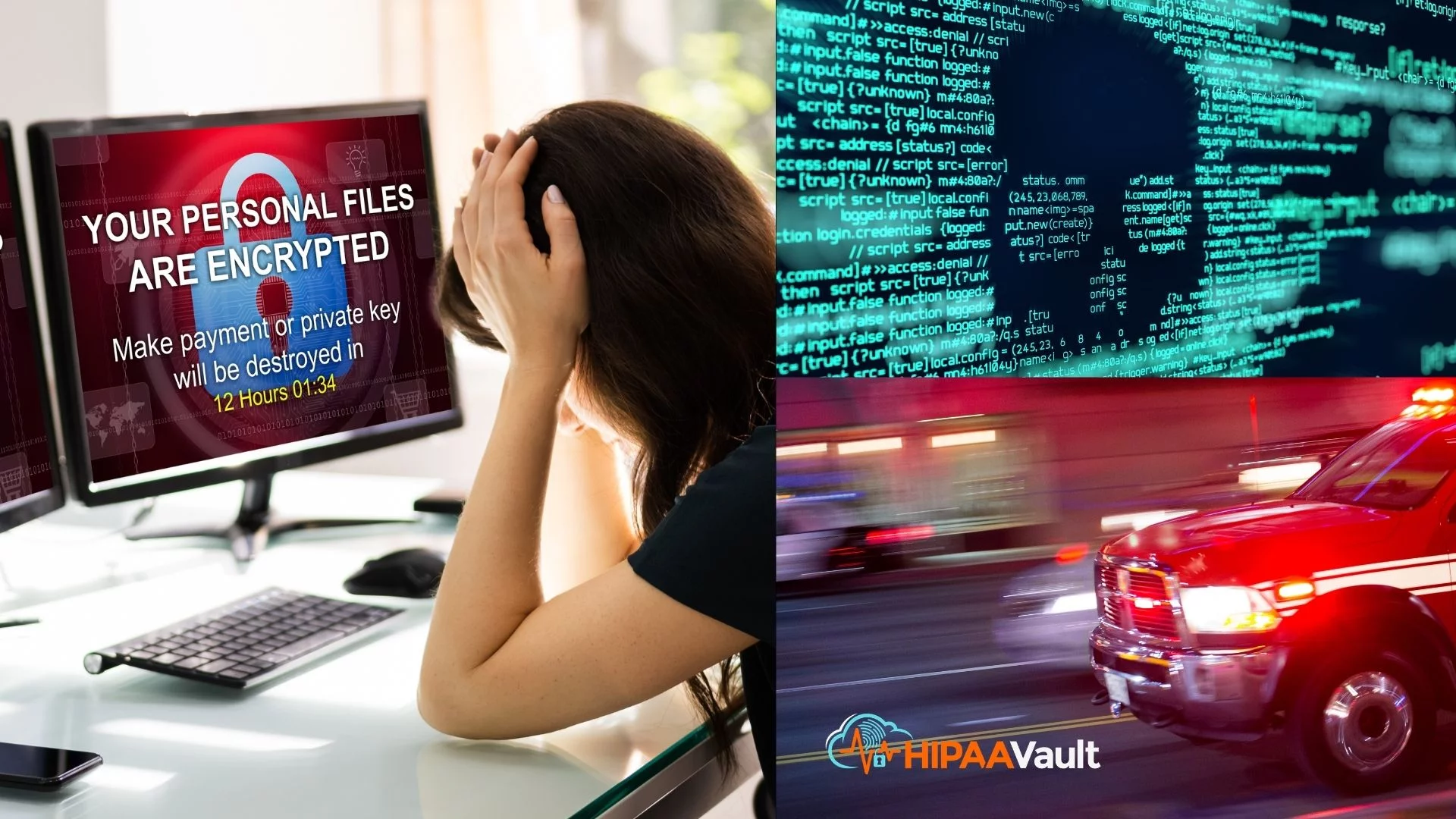
Sadly, it’s happened: As reported in the New York Times, on September 10 a woman fighting for her life was turned away from the University Hospital, Düsseldorf because hospital servers were infected with ransomware. With vital systems crashing, emergency treatment could not be administered. By the time the woman could receive services – in another hospital, 20 miles away – the hour delay resulted in her death.
Police had reached out to the attackers through information contained in the ransom note, anxious to clarify that the hospital – and not the intended target of a university linked to it – had been impacted. Although the hackers (surprisingly) agreed to stop the attack and hand over the encryption key to unlock the data, it was already too late. Authorities are now investigating possible manslaughter charges against the cybercriminals.
Unfortunately, we could see this coming. We noted how in 2017, a Vanderbilt researcher had studied increased death rates from healthcare data breaches and concluded that as many as 2100 deaths per year could be attributed to delays in needed services. More recently, with 764 US health care providers hit by ransomware attacks in 2019 (an all-time high), it appears the loss of life may even increase.
Why Hospitals?
When it comes to hospitals, cybercriminals know the stakes – as well as the potential payoffs – are high. “Hospitals can’t afford downtime, which means they may be more likely to pay — and quickly, with minimal negotiation — to restore their services,” says Brett Callow, a threat analyst at a New Zealand security firm. “That makes them a prime target.”
Unexpectedly, some cyber insurers have also played a controversial part in these decisions. While the FBI typically urges victims not to pay the attackers, these insurers have advised the opposite, since one ransom payout is often cheaper than the clean-up and recovery costs to get the data back.
How it Happens
Ransomware criminals typically target software “holes” to infiltrate healthcare systems or seek to gain access via stolen credentials – usually obtained through phishing emails. In the Düsseldorf case, German IT security officials determined that the hackers were able to breach the hospital through a hole in Citrix software that the hospital failed to update, despite a patch that had been applied earlier this year.
For typical businesses, failure to do regular security updates may result in hourly downtime costs between $140,000 and $540,000 if an attack takes the system offline. But for hospitals, the human costs of downtime – as we’ve seen from this latest incident – can be incalculable. When lives are on the line, the costs are just too high for hospitals not to pursue the best cybersecurity.
This means that those organizations who have typically relied on internal IT departments, or even a Managed Service Provider (MSP) for basic IT management and support, must realize that it’s no longer enough – especially if the MSP lacks advanced cybersecurity expertise. But doing more is often when budgetary concerns get raised.
How an MSSP can Help
Once a healthcare organization realizes the extent of their security and mitigation needs, however, they discover that it’s possible to both improve security and streamline business operations by outsourcing to a Managed Security Service Provider (MSSP). If the MSSP offers HIPAA cloud hosting (as HIPAA Vault does), capital equipment costs and IT expenditures (typically used for servers and software, onsite data centers, maintenance, etc.) can be reduced, and replaced with a more secure, efficient, and optimized environment. This is how an experienced MSSP – particularly one with HIPAA security expertise for healthcare – can actually play a partnering role going forward, once they are deemed essential to patient care.
An experienced Managed Security Service Provider (MSSP) – particularly one who has HIPAA expertise for healthcare – can actually play a partnering role in shaping a strong security plan, once it is deemed essential to patient care.
Healthcare organizations of any size that have an MSSP on their “front line” will benefit from the latest in malware and threat mitigation. MSSPs can keep abreast of and apply the latest security patches to operating systems – indispensable for preserving the integrity and availability of PHI. In addition, they provide real-time analysis of networks and logs, Security Incident and Event Management (SIEM) and alerts, managed firewalls, offsite backups, data loss prevention, and more – all important parts of a HIPAA compliant environment.
Some MSSPs – like HIPAA Vault – also offer staff training programs for cybersecurity awareness. Today’s organizations will routinely see phishing attacks, internal lapses in workstation security, USB attacks, and more. Since human errors and internal actors represent a large percentage of breaches (59%), finding an MSSP who can help provide staff training programs can be a great asset for a strong defense.
Most of the above needs are beyond most healthcare organization’s ability to manage while attempting to focus on essential services and patient care. Partnering with an experienced MSSP can free them up to do what they do best – saving lives – while ensuring critical applications and data remain available.
Want to talk to a proven healthcare MSSP? Give us a call at 760-290-3460, or look us up at www.hipaavault.com.
HIPAA Vault is the leading provider of HIPAA compliant solutions, enabling healthcare providers, business organizations, and government agencies to secure their protected health information from data breaches, threats, and security vulnerabilities. Customers trust HIPAA Vault to mitigate risk, actively monitor and protect their infrastructure, and ensure that systems stay online at all times. In addition to providing secure infrastructure and compliance for health companies, HIPAA Vault provides a full array of HIPAA solutions, including secure email, HIPAA compliant WordPress, and secure file sharing, and more.