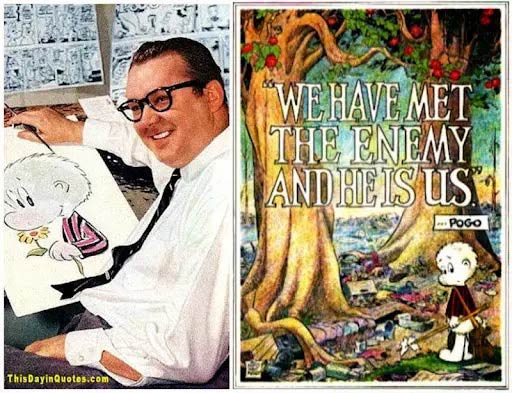
“We have met the enemy and he is us” – that great line from cartoonist Walt Kelly’s Pogo comic – was an instant classic when it first appeared in 1970 as a poster for Earth day.
Taken from the original line “We have met the enemy and they are ours,” contained in a letter from US Navy Commander Perry to Major General Harrison after the victorious Battle of Lake Erie in 1812, Kelly modified it to picture our impact on the environment:
Of course, we typically don’t like to think of ourselves as the enemy in any context; pointing away from ourselves at someone else (which leaves 3 fingers pointing back at you, as my dad used to say) feels so much better.
Yet the threat is always present, such as when we find it too easy to compare ourselves to others or open our mouths wide enough to insert our own foot.
We could go on about all the ways we shoot ourselves in the foot in life, but since it’s October and National Cybersecurity Awareness Month, we can string together our line with the first week’s theme:
“We have met the enemy and he is us…so be cyber smart.”
Not convinced the first part is warranted? No doubt, the threats originating from external attackers remain the most prevalent, yet it takes someone in your organization to provide a hole or wide-open door – often through human error and being duped – to allow it to enter.
A few statistics for you:
- 24% of employees surveyed see little or no risk in clicking a suspicious email link or attachment, demonstrating a lack of social engineering threat understanding.
- 75% of organizations globally experienced a phishing attack in 2020, and 96% came by email.
- 68% of organizations, in general, say they feel vulnerable to insider attacks, and 63% point the finger at privileged IT users as the greatest risk, according to a Cybersecurity Insiders report.
- 78% of organizations doubt they have effective management of user privileges.
- 87% would find it difficult to determine the actual damage of an insider attack.
Concerning the healthcare industry,
- 48 percent of healthcare breaches were insider-related in 2020. Healthcare was the leading industry for internal bad actors according to a 2020 Verizon report.
- 36% of errors are due to Misdelivery (basic human error) of electronic or paper documents, notes the 2021 Verizon Data Breach Report
- 32% of hospital staff have never received proper cybersecurity training, according to this security playbook for hospitals.
With stats like these, it becomes easier to understand how the average cost of a healthcare data breach is now $9.4 million.
In this first week of Cybersecurity Month 2021, we therefore urge all organizations (healthcare especially) to recognize that the internal threat is quite real and to prioritize both zero trust security and staff training.
We’ve discussed a zero-trust approach to security in the past, which you can check out here. It’s an approach that jettisons the old “castle and moat” perimeter security as sufficient, and takes seriously that the dangers can come from within your own organization; that we “have met the enemy and he is us.”
HIPAA Vault’s Zero-Trust approach to security is present in all of our HIPAA-compliant solutions. From our secure hosting to compliant WordPress and email, we design in features like user access controls and two-factor authentication, end-to-end encryption, and more.
Talk to us today to learn more! 760–394–6920 or chat us at www.hipaavault.com.
HIPAA Vault is a leading provider of HIPAA-compliant solutions, enabling healthcare providers, business organizations, and government agencies to secure their protected health information from data breaches, threats, and security vulnerabilities.







