Extortion as a Service? It’s the name of the game for ransomware actors like REvil. But how did it all begin?
The July 3rd ransomware attack on software company Kaseya by the Russian-based REvil gang is considered by some measures to be the world’s largest ever, impacting supermarket chains in Sweden and schools in New Zealand.
Taking ransomware-as-a-service to new heights (or lows), REvil essentially acts as a business by selling hacking technology to third-party hackers. Before the Kaseya attack, they were responsible for less than 10% of known ransomware victims. Now that number has ballooned to 42%.
At least 60 customers who had deployed Kaseya’s popular VSA software on-premises were impacted “upstream,” many of which were Managed Service Providers (MSPs).
The “downstream” impact was even more significant: REvil gained access to the MSP’s servers and managed to push their ransomware out to the approximately 1,500 businesses the MSPs served.
HIPAA Vault was not impacted by the attack.
Ransomware: How it All Began
From classic mafia protection schemes to white-collar crime, extortion is as old as the hills. You might wonder, however, how the idea of “digital ransomware” was first conceived. The truth is stranger than a Hollywood movie.
In 1989, Dr. Joseph L. Popp was a Harvard-educated evolutionary biologist and a consultant for the World Health Organization in Kenya. Active in AIDS research, some believe Popp’s strange behavior began when he was passed over for a job at the WHO.
Whether embittered by the (perceived) slight or actively planning to change current AIDS policy, Popp conceived a disturbing plan: 20,000 ransomware floppy disks, to be sent to attendees of the WHO AIDS conference under the guise of informational software.
The ‘AIDS trojan,’ as it was called, would activate after a computer was booted 90 times, then lock up or encrypt the user’s files on their C drive. To solve the issue, users would be required to send $189 to PC Cyborg Corporation at a PO box in Panama.
Here is the original message that Popp’s victims saw:
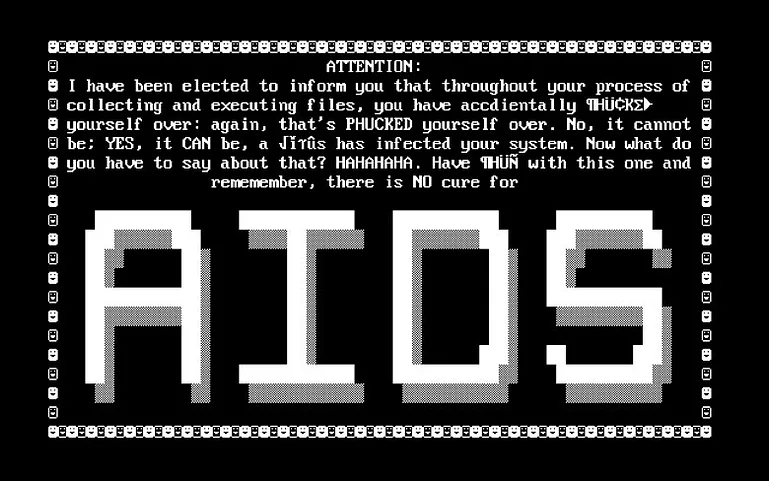
Like the AIDS virus itself, fear spread quickly among those who saw their directories disappear and files lock up. Many deleted their hard drives unnecessarily, despite the fact that decryption tools to handle Popp’s simple symmetric cryptography were soon available. Despite this fact, much important research was lost.
Eventually, Popp was tracked down by the British anti-virus industry and charged with blackmail. After exhibiting some further odd behaviors (like wearing a cardboard box on his head and curlers in his beard to ward off threats of radiation) he was judged unfit to stand trial and wound up back in the US.
Popp went on to self-publish a book entitled “Popular Evolution” which detailed many of his radical ideas on reproductive issues. He later created a butterfly conservatory in upstate New York and promised to donate all profits from the malware to fund AIDS research before he died in 2007.
Ransomware Today
It’s certainly ironic for ransomware to have sprung up during a global epidemic, since today, it has become something of an epidemic itself. When modern-day actors like REvil can now demand $70 million from an influential software company Kaseya, extortion via ransomware shows no signs of slowing. Unfortunately, our recent pandemic also seems to have spurred its growth.
Notably, the other major attack of 2021 – the Colonial pipeline ransomware attack on May 7 – also appears to be the work of Russian actors. An organization known as DarkSide demanded a $5 million ransom from Colonial, which they subsequently paid in order to recover files and limit damages. U.S. law enforcement eventually recovered $2.3 million in bitcoin from the hackers.
In a call with Russian President Putin, President Biden vowed to take “any necessary action” to protect US interests, and “underscored the need for Russia to take action to disrupt ransomware groups operating in Russia” according to a statement – even if they may not be state-sponsored groups.
How to Respond
Clearly, no one could’ve imagined the Pandora’s Box that Popp opened through his malicious code, and the rise of gangs like REvil.
For those impacted by the Kaseya attack, the FBI and Federal Cybersecurity Agency are recommending that managed service providers and their customers download the Kaseya VSA detection tool, which analyzes a system and determines whether there are any indicators of compromise. The process of securing VSA servers is more fully detailed in the Kaseya On-Premises Startup Readiness Guide.
Victims should also “enable multi-factor authentication for every account under Kaseya’s control and to limit communications with remote monitoring and management capabilities to known IP address pairs,” according to Becker’s Health IT.
In general, it behooves all MSPs and healthcare organizations to also have a detailed incident response plan for responding to a ransomware event. Creating a policy for suspicious emails and ensuring all users are made aware of procedures is also vital.
Additional, strategic measures for fighting ransomware are included in HIPAA Vault’s compliant hosting, like centrally-managed anti-malware solutions and an Intrusion Detection System (IDS). Advanced spam filtering, regular, offsite system backups, password management policies, and multi-factor authentication are also standard.
Fighting ransomware is now a necessity for healthcare organizations. To that end, prioritizing data security and finding the right HIPAA Compliant hosting provider is key.
If you have any questions on HIPAA data security or any of the services we provide, please contact us! 760-290-3460.
HIPAA Vault is a low-cost leader of HIPAA compliant solutions, enabling healthcare providers, business organizations, and government agencies to secure their protected health information from data breaches, threats, and security vulnerabilities.







